Core Banking Vendor Due Diligence Checklist for Regulated Fintech
Summary
Core Banking Vendor Due Diligence in 60 Seconds
- Choosing a core banking vendor is a long-term strategic bet: the platform shapes compliance posture, integration speed, unit economics, and how painful migration will be later.
- Most costly failures trace back to hidden architectural limits, opaque compliance coverage, weak security evidence, or contract terms that cement dependency—not a bad product roadmap alone.
- This checklist frames procurement like enterprise buyers do: evidence over slides, cross-functional review (CTO, CIO, procurement, vendor risk), and explicit exit strategy.
- Evaluate architecture and APIs, regulatory readiness, security operations, ecosystem fit, total cost of ownership, SLAs, and data portability before multi-year commitments.
- Strong due diligence early reduces rework, regulatory surprises, and emergency migrations; weak diligence shows up as incidents, audit findings, and stalled roadmaps.
- DashDevs helps teams stress-test vendor choices alongside custom banking and integration delivery—so the stack you buy matches how you will actually operate.
Selecting a core banking platform is one of the highest-leverage decisions a regulated fintech will make—and one of the easiest to rush. The sections below mirror how serious enterprise buyers run procurement: clear questions, explicit evidence, and shared ownership across technology, risk, and commercial teams.
If you need grounding on what “core” actually does in modern stacks—not only legacy mainframe stereotypes—start with what is core banking before you normalize vendor shortlists.
TL;DR for CIOs and procurement leaders
What this decision really is
Choosing a core banking vendor is not simply a technical bake-off. It is a long-term strategic risk decision that shapes your license story, product velocity, integration cost, and how painful migration will be if the relationship sours.
Speed to market matters, but teams that optimize only for launch often discover hidden architectural constraints, compliance gaps, or vendor lock-in when they try to scale, enter a new region, or ship the next major product line.
“Procurement is where optimism meets the balance sheet. The core is where optimism meets the ledger.”
Most expensive failures do not start with building the wrong customer experience. They start with infrastructure that cannot support the operating model the business eventually needs—whether that is real-time ledger behavior, granular reporting for supervisors, or safe exit to another stack.
What you get from this article
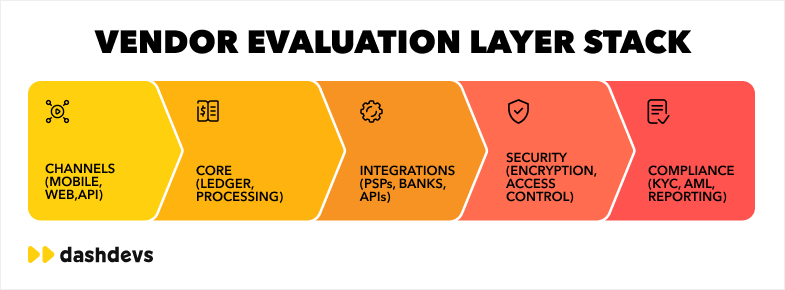
This article provides a structured, procurement-ready checklist spanning architecture and scalability, security, compliance, integrations and ecosystem fit, cost and total cost of ownership, and exit strategy.
Use it to align CTOs, CIOs, procurement, and vendor risk teams around the same facts before signatures land on a multi-year agreement. Early due diligence is not bureaucracy; it is how you avoid paying for the same decision twice—in rebuilds, incidents, and emergency remediation.
| Stakeholder | Primary question to answer before sign-off |
|---|---|
| CTO / VP Engineering | Can we integrate, observe, and change this system without vendor-only priests? |
| CIO / Platform | Can we run releases, DR, and capacity with clear ownership and SLAs? |
| Procurement / vendor risk | What are we locked into commercially, legally, and operationally? |
| Compliance / MLRO | Can we evidence controls end-to-end for our license and regions? |
| CISO / security | Is the control story testable—not narrative-only? |
Quick signals that diligence was shallow
- Roadmap answers replace evidence (no diagrams, no test results, no references).
- Compliance is described as a checkbox without mapping to your license class.
- Pricing is a single line item with “platform fee” and no unit economics model.
- Exit is “we’re partners” instead of data formats, timelines, and fees.
Starting point
The launch that quietly caps your second act
Picture a regulated fintech that launches on a vendor stack in nine months. Cards work, accounts open, and the board celebrates time to market.
Eighteen months later, the same team wants multi-currency accounts, a new lending product, and expansion into a neighboring market. Suddenly the core struggles: batch-oriented settlement, API gaps, unclear audit trails, or regional coverage that exists on a slide but not in production. Integrations that looked “available” turn out to be partner-specific projects with long queues. Compliance asks for reporting the platform was never designed to produce cleanly.
That pattern is common because core banking systems sit at the center of money movement, ledger truth, product configuration, and operations. They are deeply embedded—not a peripheral SaaS tool you can swap in a quarter.
Once customer balances, transaction history, fee logic, and support workflows are wired in, replacement becomes a program, not a project. Yet many teams underestimate vendor risk in the early stage and overweight demo features and onboarding promises.
If you are also weighing BaaS or embedded models alongside a core decision, choosing your BaaS provider: a comprehensive checklist is a useful parallel lens—sponsor-bank and distributor relationships add another layer of dependency.
Why “we’ll fix it later” rarely works
| Phase | What teams assume | What usually happens |
|---|---|---|
| MVP | “We only need basic accounts + cards.” | Ledgers, fees, and exceptions become product truth—hard to unwind. |
| Growth | “We’ll add lending / FX later.” | Posting models and reconciliation windows collide with new products. |
| Expansion | “The vendor supports that region.” | Data residency, scheme rules, and reporting differ materially. |
Vendor lock-in is not an abstract concern. It shows up as proprietary integration patterns, data you cannot export cleanly, contract terms that make migration punitive, and engineering teams who only know how to operate one black box.
How to avoid vendor lock-in traps walks through how that dependency usually forms—before contract language makes it expensive to unwind.
“Most fintech failures don’t come from building the wrong product — but from choosing the wrong infrastructure.”
This article does not replace your legal review or security assessments. It mirrors how enterprise buyers evaluate core vendors in real procurement cycles: structured sections, evidence requests, and red flags you can discuss in the same room as your RFP scorecards.
Why Core Banking Vendor Selection Is a Strategic Risk Decision
What “core” anchors inside your company
A core banking system defines more than “where balances live.” It shapes product flexibility, compliance posture, scalability, partner integrations, and long-run cost.
Unlike a standalone CRM or analytics layer, the core is tightly coupled to operations: settlement cutoffs, reconciliation, dispute handling, AML monitoring hooks, and the reports regulators expect.
When those assumptions are wrong, you do not get a small inconvenience—you get roadmap friction, audit findings, or an expensive re-platforming program.
“The core is not a vendor choice. It is the template your risk, finance, and product teams will argue inside for a decade.”
That is why this decision belongs in the same conversation as capital allocation and multi-year strategy.
A vendor that fits a narrow MVP may not fit multi-entity structures, new licenses, or scheme changes.
The migration cost rises non-linearly with volume, product surface area, and organizational dependence on bespoke workarounds.
| Risk category | Early symptom | Late-stage symptom |
|---|---|---|
| Architecture | Slow partner integrations | Re-platform or parallel “shadow core” work |
| Compliance | Manual reporting | Audit findings, remediation programs |
| Commercial | Opaque pricing | Margin compression at scale |
| Lock-in | No export discipline | Emergency renewal negotiations |
DashDevs sees this dynamic in delivery programs where architecture and vendor boundaries are explicit from day one. The digital banking platform case illustrates how onboarding, KYC, and account infrastructure interact with everything downstream.
In those environments, core and integration choices directly affect whether you can scale, integrate safely, and comply without building a parallel shadow system.
If your organization is comparing build, buy, or hybrid paths, align the discussion with how you will deliver over time. Fintech software development covers end-to-end execution once the target model is clear.
For platform and distributor strategy—not only core mechanics—how to build a neobank using vendors, platforms, or APIs pairs naturally with this checklist.
You are not choosing a logo for a slide. You are choosing the foundation your teams will build on for years.
How to Use This Due Diligence Checklist
In each section, you will find practical questions to ask vendors, the type of evidence to request (documentation, diagrams, certifications, references), and signals that often indicate risk—vagueness, hand-waving, or “available on the roadmap” without a named delivery path.
Who owns what (RACI-style)
| Workstream | Primary owner | Supporting owners |
|---|---|---|
| Architecture & APIs | CTO / VP Engineering | Solution architects, SRE |
| Compliance mapping | MLRO / Compliance | Legal, product |
| Security evidence | CISO / security lead | IT risk, vendor risk |
| Commercial & exit | Procurement | Legal, finance |
| Operations & SLAs | CIO / platform | Incident management |
Treat the checklist as a collaboration tool. CTOs and engineering should own architecture and API truth. CIO and platform leaders should own operations, SLAs, and change management. Procurement and vendor risk should own commercial terms, exit, and subprocessor transparency. Compliance and security should challenge anything that sounds like policy without controls.
Before you lock scoring criteria, it helps to pressure-test stack assumptions with solution architecture services—so procurement chases evidence, not adjectives.
If leadership wants an independent facilitator for the process itself, fintech consulting is often engaged alongside internal procurement teams.
When you need a structured scope exercise before vendors enter the room, product discovery service work can align product, risk, and architecture assumptions so scoring tracks reality.
Evidence over narrative: a minimum pack
- Current reference architecture (not a marketing diagram from 2019).
- API catalog + deprecation policy + sample OpenAPI where claimed.
- SOC (or equivalent) + latest pen-test executive summary + incident stats (even ranges).
- DR and RTO/RPO commitments in writing.
- Data export samples for balances, transactions, and configuration.
The goal is not to produce a beauty contest between sales decks. It is to surface hidden constraints before a long-term contract locks you into a system that cannot support how your business will actually run.
“If it isn’t written down and testable, it isn’t a control—it’s a hope.”
Architecture and Scalability Evaluation
Architecture is the highest-signal chapter in core banking vendor evaluation because it determines what you can change later—and at what cost.
Flexible systems separate concerns: ledger logic, product configuration, channels, and integrations are bounded and documented. Rigid systems blur those boundaries: a “small customization” becomes a vendor project, a release dependency, or a performance surprise under load.
Modular vs monolithic: what to ask
Start by clarifying modularity versus monolith. A modular core exposes clear domains—accounts, balances, interest, fees, limits, postings—with contracts between them.
A monolithic core may still work for a narrow launch, but tight coupling often shows up as long release cycles, unclear failure domains, and scaling strategies that amount to “buy bigger boxes” instead of isolating hot paths.
Ask for reference architecture diagrams that match your jurisdiction and product scope, not a generic marketing drawing.
| Question | Strong answer | Weak answer |
|---|---|---|
| How are domains bounded? | Clear boundaries, contracts, ownership per team | “Everything is flexible” |
| How do you ship changes? | Release trains, feature flags, compatibility policy | “We schedule upgrades for you” |
| What happens under load? | Isolated scaling, backpressure, SLOs | “We handle scale” |
APIs, events, and real-time expectations
APIs deserve scrutiny beyond “REST exists.” How are idempotency, versioning, and backward compatibility handled?
Are webhooks or event streams first-class for the workflows you need—real-time balance updates, payment status, exceptions—or will you poll and reconcile forever? Real-time processing is not a buzzword; it is a product requirement when customers expect instant feedback and operations need intraday control.
Ask for performance benchmarks under realistic mixes (reads vs writes, burst vs sustained) and for capacity planning assumptions tied to tenant growth.
Evidence to request includes API catalogs, OpenAPI specs where available, integration playbooks, disaster recovery runbooks, and load test summaries.
Red flags include missing documentation, undocumented “side channels” for critical flows, shared database tables that couple unrelated products, and scaling stories that skip data partitioning or regional deployment models.
Data model and posting integrity
Ledger and posting semantics are where “small” product decisions become big engineering problems. Confirm how double-entry (or equivalent) integrity is enforced, how posting reversals work, how timezone and cutoff rules are applied, and how backdated or corrective entries are audited.
If the vendor cannot explain reconciliation between channel and core in plain language, you will pay for that ambiguity in operations and finance later.
“Architecture decisions made during vendor selection will define your ability to scale for years.”
These are not short-term annoyances. Tightly coupled services turn every new product into a coordination tax. Unclear scaling strategy becomes an emergency when volume jumps after a partnership or marketing win.
For how banking stacks evolve structurally as products grow, see fintech architecture.
Channel behavior in production—what users and ops actually see—is covered well in the mobile banking app development guide.
When you need engineering capacity to align delivery and observability with the core you pick, backend development services are the usual complement to vendor-led infrastructure.
Compliance and Regulatory Readiness
Compliance is not a module you bolt on after go-live. In regulated fintech, it is part of system design: who can move money, how transactions are recorded, what audit trails exist, and how reports are generated for supervisors and partners.
A core that cannot evidence those behaviors forces manual workarounds—spreadsheets, shadow ledgers, brittle exports—that auditors and regulators are trained to find.
Map the license, then the controls
Start from your license footprint and roadmap. EU, US, and MENA regimes differ in AML expectations, data residency, open banking norms, and reporting cadence.
The vendor should articulate which controls are native, which rely on configuration, and which depend on partner systems—KYC vendors, fraud tools, screening services—not a vague “we support compliance.”
| Control area | Evidence to request | Typical gap |
|---|---|---|
| Customer risk lifecycle | Tiering model, EDD triggers, audit trail | “KYC is handled by integration partner” with no core linkage |
| Transaction monitoring | Event hooks, screening outcomes, case IDs | Monitoring only in channel, not reconciled to postings |
| Reporting | Sample regulatory extracts, lineage to ledger | Rebuilt manually in BI |
Operational workflows, not only policies
Verify support for customer lifecycle tied to risk tiering, transaction monitoring hooks, sanctions screening integration points, STR/SAR-style workflows where applicable, and immutable audit logs for money movement.
Reporting should be traceable to ledger postings, not reconstructed from channel logs.
“Compliance is not a PDF library. It is the ability to show your work under stress.”
Evidence should include certifications and audit reports where relevant (for example SOC-style reports), regulatory documentation packs, sample supervisory reports, and reference customers in similar license classes.
Transparency gaps are red flags: “trust us,” NDA-only answers for basic control questions, or custom compliance priced as black-box professional services without deliverables.
DashDevs sees the same pressure in regulated connectivity programs where orchestration has to survive scrutiny—the Tarabut gateway case is one example of that pattern.
Adjacent to most cores, customer identity work is rarely optional in practice. KYC services belong in the same diligence thread as ledger and reporting.
For US market questions, the ultimate guide to US fintech regulations works as a prompt list to take into vendor sessions—complementing your counsel, not replacing it.
If compliance answers do not survive a joint session with legal and risk, treat that as stop-sign material—not a sales objection to overcome with optimism.
Security and Risk Management
Security is not only encryption at rest. For fintech infrastructure, it is identity and access control, key management, network segmentation, logging and monitoring, fraud detection hooks, vulnerability management, and incident response.
Regulators treat breaches as both technical and reputational events—your vendor story has to hold up in both dimensions.
Design-time vs run-time security
Procurement teams should validate how sensitive data is classified, where it resides, and which encryption standards apply end-to-end.
Ask how secrets are managed, how admin access is logged, and how privilege elevation works in production.
Vendor SOC reports are a starting point, not the entire story—push for penetration testing summaries, threat modeling artifacts for major releases, and patch SLAs for known vulnerabilities.
| Topic | Ask | Red flag |
|---|---|---|
| Key management | HSM/KMS model, rotation, who can decrypt | Shared long-lived keys across environments |
| Segmentation | Network zones for admin vs app vs data | “VPN access available on request” |
| Logging | Tamper-evidence, retention, SIEM export | Logs only in vendor UI without export |
Incidents are regulatory events
Operational security matters as much as design. Incident response should include notification timelines, customer communication templates where required, forensic support, and post-incident reviews with root-cause accountability.
Weak security becomes regulatory risk when supervisors conclude controls were not fit for purpose.
“A breach is never only technical. It becomes a story about governance.”
Independent validation should be on your roadmap too.
DashDevs provides penetration testing services to stress applications and integrations beyond vendor claims—especially where custom glue code sits between channels and core.
For committee-level vocabulary on threats, cybersecurity in banking: main threats and challenges is a practical primer to read beside your vendor’s control matrix.
For a tighter narrative on how banks organize defenses, banking and cybersecurity: how to avoid threats is a shorter companion read for non-security executives.
Use all of that evidence alongside your vendor’s specific control narrative—not instead of it.
Integration and Ecosystem Compatibility
Modern fintech products are graphs of providers: payment schemes, card processors, KYC vendors, open banking aggregators, FX, ledger bridges, and internal data platforms.
A core that cannot integrate cleanly becomes the bottleneck that slows every roadmap bet.
Integration patterns, not partner logos
Vendor evaluation should demonstrate integration patterns, not logos on a slide. Request API documentation for extension points, sandbox behavior, webhook reliability, and error semantics.
Ask for uptime metrics, maintenance windows, and backward compatibility policies—your release train should not break because a vendor deprecated a field without notice.
| Integration class | What “good” looks like | What “bad” looks like |
|---|---|---|
| Payments / schemes | Idempotent APIs, clear state machine | Opaque status codes + manual ops |
| KYC / fraud | Webhooks + case correlation IDs | CSV drops + nightly sync only |
| Data warehouse | CDC or batch with watermarking | One-off dumps |
Proprietary APIs and limited partner ecosystems increase dependency and timeline risk. Feature parity lists rarely capture that pain; integration throughput does.
A strong ecosystem—documented patterns, certified connectors, living sandboxes—is often more valuable than a longer feature matrix today.
“The best feature list loses to an integration that ships in two sprints.”
Map your roadmap to fintech integrations discipline so commercial and engineering share the same integration vocabulary.
API in banking: the guide to bank APIs gives buyers shared language before integration workshops turn into slide comparisons.
Payment orchestration expectations usually sit next to that work—payment gateway services is a common lens when you compare vendor claims to operating reality.
Vendor Lock-In and Exit Strategy
Vendor lock-in is one of the most underestimated risks in fintech because it compounds quietly.
Migration is expensive once balances, history, product parameters, and operations playbooks are entangled with a single stack. Boards notice lock-in when pricing increases at renewal, strategic initiatives stall, or due diligence for fundraising exposes opaque dependencies.
Data, config, and operational knowledge
Evaluate data ownership in plain language: who owns customer records, transaction history, configuration, and audit logs?
What export formats exist, how complete are they, and how often are they tested in practice—not theoretically?
Contract terms should define transition assistance, API access during migration, escrow or continuity mechanisms where appropriate, and exit fees that cannot surprise you after sunk-cost bias sets in.
| Exit workstream | Minimum clarity |
|---|---|
| Balances & postings | Canonical export schema, reconciliation proof |
| Product config | Versioned parameters, not UI-only state |
| Integrations | Partner credentials handoff, webhook replay strategy |
| Ops runbooks | What your team must re-learn on a new stack |
Contract mechanics that matter
- Termination for convenience vs for cause—and what changes if your license scope shifts.
- Step-in assistance: named deliverables (e.g., export jobs, read-only API period).
- Benchmarking and most-favored clauses where commercially realistic.
Negotiation playbooks that reduce dependency before signature overlap with the moves in how to avoid vendor lock-in traps.
Mapping exit paths early is also architecture work—not only legal work. Solution architecture services help teams document what must be portable before emotions run high at renewal.
If exit strategy is missing from vendor materials, treat that as dependency risk, not neutrality.
“A vendor who cannot describe exit is describing capture.”
Cost Structure and Total Cost of Ownership
List price is the smallest part of the truth.
Total cost of ownership includes implementation, integrations, environment fees, per-transaction charges, premium support, change requests, training, internal engineering time, and operational overhead when things break outside business hours.
Build a TCO model, not a quote comparison
Vendors should provide transparent pricing models with clear breakdowns: minimums, overage rules, indexation, true-up mechanics, and what is not included. Unclear pricing—bundled “platform” fees without usage definitions—is a common red flag because it hides margin risk you will pay later.
| TCO bucket | Examples | Questions |
|---|---|---|
| License / SaaS | Per account, per txn, per env | What happens at 10× volume? |
| Professional services | Implementation, migrations | Fixed scope vs time-and-materials? |
| Change | Custom features, new schemes | Who owns backlog priority? |
| Run | Support tier, on-call, incident credits | What is excluded from “standard”? |
How much does it cost to build an app frames build-versus-buy economics when leadership wants outside benchmarks.
Banking app development cost in 2026 adds banking-specific bands that sit next to core spend—channels, compliance, ops—as you turn list price into a multi-year model.
Evaluate cost always alongside flexibility: a cheaper core that caps roadmap velocity is not cheap.
“TCO is where CFOs discover the difference between a demo and an operating system.”
Vendor Support and Operational Reliability
Downtime in fintech is not only engineering embarrassment—it is revenue, trust, and sometimes regulatory attention. Support and operational reliability belong in the same weight class as architecture.
SLAs: what must be in the contract
Ask for SLA commitments with measurable targets: availability, response times, severity definitions, escalation paths, and credits or remedies when SLAs miss.
Incident handling should be documented: runbooks, communication protocols, postmortems, and fix cadence for known defect classes.
For many regulated products, 24/7 coverage is not luxury—it is table stakes when money movement fails on weekends.
| Severity | Example trigger | Response expectation |
|---|---|---|
| S1 | Money movement halted for many users | Immediate bridge, exec comms path |
| S2 | Major degradation | Workaround within hours |
| S3 | Minor defect | Ticketed within business SLA |
Operational reliability also means change management: how releases land, how breaking changes are communicated, and whether your team gets early visibility into maintenance windows.
A vendor that ships fast without predictable operations will consume your internal capacity endlessly.
Release governance is often where buyer-side engineering shows up. Cloud and DevOps services are a common pairing when you negotiate who operates pipelines and environments.
For how delivery contracts translate into day-to-day practice, DevOps as a service is a useful reference thread alongside SLA reviews.
- Customer-facing status pages and internal incident portals—prefer both with aligned truth.
- Root-cause transparency for repeated incidents: pattern failure is a vendor maturity signal.
Real-World Case Insights from DashDevs
DashDevs builds and integrates fintech platforms where regulated rails, complex workflows, and scalable infrastructure must coexist.
The Downing investment management work illustrates demanding financial product requirements paired with delivery discipline.
The InABLR investment platform case shows how investment UX, state clarity, and trust mechanics matter when users move meaningful value.
What these cases imply for vendor diligence
- State and lifecycle clarity (pending, settled, failed) must match core posting semantics—or support and finance will disagree on truth.
- Partner integrations (brokers, custodians, market data) surface the same questions as core banking vendor reviews: APIs, idempotency, reconciliation, audit evidence.
- Delivery discipline is a proxy for whether your own team can operate complex stacks—if vendor ops are opaque, you inherit that opacity.
Across programs like these, vendor evaluation and custom development are not opposites.
Teams need partners who can read a core vendor architecture critically, challenge integration assumptions, and ship software that fits the operating model—not only slides.
When you mix vendor cores with custom channels, Fintech Core is a compact way to see how capabilities fit together before you lock scope.
CIO and Procurement Checklist Summary
Before you normalize a shortlist, pressure-test whether you have answers—not assertions—across six pillars. If the list reads like feature marketing, reset expectations with open banking solutions as a reminder that ecosystem claims must map to concrete integration paths.
When you score finalists, keep how to avoid vendor lock-in traps nearby—exit realism belongs in the same room as architecture scores.
- Architecture and scalability: modularity, API truth, real-time needs, evidence of performance under load.
- Compliance and regulatory readiness: license fit, audit trails, reporting, artifacts that survive review.
- Security and risk management: controls, testing, incident readiness—beyond a single SOC report.
- Integrations and ecosystem: documented patterns, partner velocity, uptime and change policies.
- Cost and TCO: transparent commercials, internal operating cost, flexibility trade-offs.
- Exit strategy and lock-in: data ownership, export, transition terms, credible migration path.
One-page mental model
| Pillar | “Green” signal | “Red” signal |
|---|---|---|
| Architecture | Versioned APIs, bounded domains | Mystery integrations |
| Compliance | Traceable reports to ledger | Manual supervisor rebuilds |
| Security | Testable controls, pen-test cadence | SOC-only narrative |
| Integrations | Partner playbooks, sandboxes | Logo slides |
| TCO | Unit economics at scale | Opaque platform fee |
| Exit | Tested exports, transition terms | Exit fees undefined |
Vendor evaluation is due diligence for governance, not paperwork for procurement alone.
Conclusion
The window where core vendor choice is cheap to fix closes fast.
Mistakes at this stage are costly because they embed in product logic, operations, partner contracts, and customer trust. Remediation later means migration programs, dual-run costs, and teams diverted from growth work.
Treat due diligence as insurance against a class of failure that does not announce itself at demo time.
If you want an external review before signature, fintech consulting is often used to stress-test the shortlist against how you will actually run the bank—not how the vendor sells it.
Final reminders
- Vendor sales teams optimize for signature; your team optimizes for operability at scale—tension is normal.
- Evidence beats roadmap slides; roadmaps belong in contracts as options, not promises.
- Bring finance and ops into architecture sessions early—ledger truth is a shared language.
“The cost of choosing the wrong core banking vendor is not just financial — it limits your ability to scale, adapt, and compete.”

