How to Build a Fiat-Crypto Platform With a Unified Balance System
A practical infrastructure guide for fintech founders, CTOs, and product teams designing unified fiat and crypto operations at scale
Summary
What You Need to Know in 60 Seconds
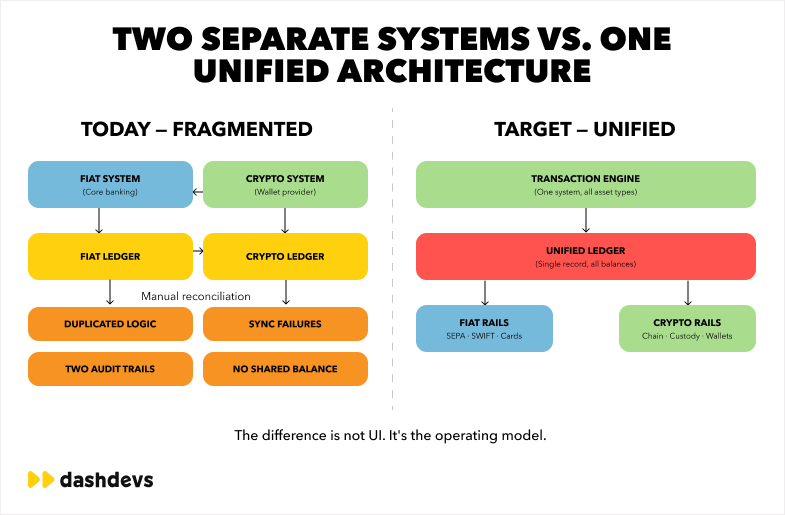
- The hardest part of hybrid finance is not adding crypto rails, but unifying operations across fundamentally different transaction models.
- A modern fiat crypto platform needs one orchestration layer, one financial truth layer, and one operational model across providers and rails.
- If fiat and crypto ledgers remain siloed, treasury, reconciliation, support, risk, and accounting teams will absorb continuous operational friction.
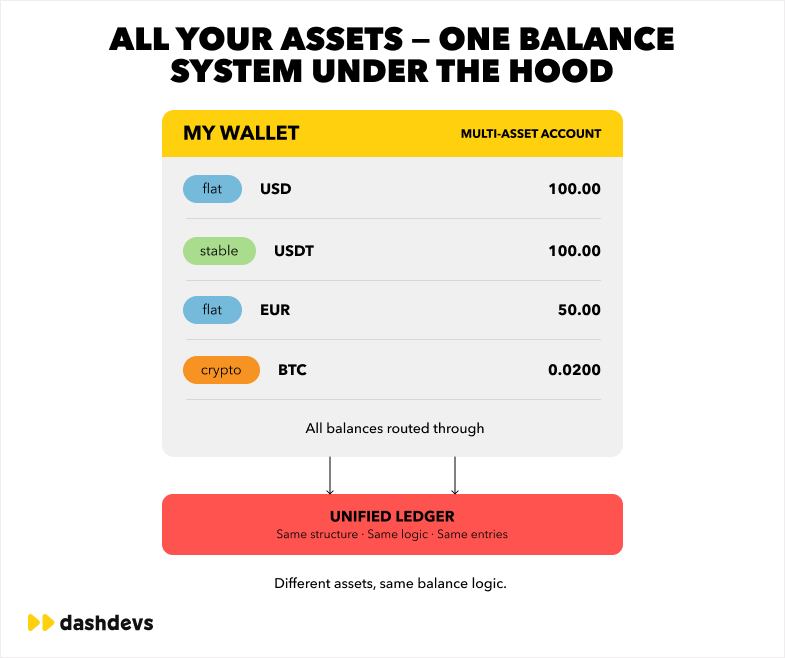
- A unified balance system helps normalize settlement timing, transaction states, and accounting compatibility without hiding critical risk controls.
- DashDevs and Fintech Core focus on orchestration-first, ledger-centric architecture for fintech platforms that need to scale without operational fragmentation.
If you are asking how to build a fiat crypto platform, the first strategic decision is not wallet UX, token support, or exchange spread logic. The first decision is operational: how your product will maintain one consistent financial reality across rails that settle differently, fail differently, and report differently.
Most teams can connect a fiat PSP and a crypto transfer service quickly. The failures begin later, when finance asks for one balance view, support asks for one transaction history, compliance asks for one audit trail, and product asks for one predictable customer experience. This is where architecture quality decides whether a platform scales or accumulates operational debt.
This article explains how modern platforms approach building fiat crypto platform operations with orchestration-first architecture, unified ledger logic, and accounting normalization. It is written for operators who need systems that survive real traffic, real incidents, and real reporting obligations.
Summary
Before the deep dive, here is the practical takeaway:
- The problem is not supporting crypto rails; the problem is unifying operations across different financial rails.
- A fiat crypto platform needs one orchestration model, not one-off connectors.
- A unified balance system must reconcile event timing differences, not only aggregate balances.
- Treasury and accounting compatibility should be designed from day one.
- Provider abstraction protects product velocity and reduces vendor lock-in over time.
1) Operational Fragmentation Is the Real Failure Mode
The most common misconception in hybrid finance is that complexity lives in blockchain integration. In production, complexity lives in operations. A fiat processor may confirm instantly and settle later. A blockchain transfer may have deterministic finality rules but uncertain confirmation timing under congestion. Internal support and finance teams still need one answer for “what happened” and “what is the current balance state.”
When those worlds stay separate, the platform becomes two businesses pretending to be one. Customer support sees one transaction in a PSP dashboard and another in a chain explorer. Treasury sees unaligned inflow/outflow windows. Accounting sees non-normalized states that do not map cleanly to journal rules.
Fragmented cash flow and fragmented truth
A fragmented stack creates fragmented cash flow dynamics. Fiat funding may hit in batched settlement windows while stablecoin movements can complete at variable block intervals. If the platform treats those as separate realities, teams end up with shadow spreadsheets, manual offsets, and disputed balances.
This problem compounds with growth. The larger the platform, the more “small exceptions” become a structural burden. Refund race conditions, delayed callbacks, chain reorg handling, and provider-specific status codes all leak into operational workflows.
Treasury blind spots and support escalations
Treasury blind spots appear when balances are “technically correct” in each subsystem but operationally inconsistent at platform level. A user may see available funds while treasury marks them pending. A merchant may trigger payout before finality thresholds are met. These are not edge cases in high-volume systems; they are routine if architecture is fragmented.
Support escalations then become expensive because investigators cannot rely on one transaction narrative. Instead of one timeline, they reconstruct cross-system events manually. That is costly, slow, and risky when regulatory reporting windows are tight.
“As fintechs evolved, their once-simple models became multi-layered ecosystems.” — Fintech Garden episode 122
2) Fiat and Crypto Follow Different Transaction Models
A resilient crypto fiat platform starts by accepting that fiat and crypto are not just different rails. They are different transaction models with different assumptions about finality, reversibility, dispute mechanics, and settlement windows.
Fiat flows are typically account-based and intermediary-driven. Crypto flows are chain-state-driven and confirmation-dependent. Treating them as if they share one lifecycle without normalization creates state chaos in product and operations.
Account-based rails vs confirmation-based rails
In account-based fiat rails, transaction states are usually mediated by one or more institutions: issuer, acquirer, processor, settlement bank. Reversals and disputes are part of the model. In chain-based rails, transfer validity and settlement depend on network confirmation and transaction inclusion.
This difference matters for customer-facing logic. A “successful transfer” in one rail may still be operationally pending in another context. If your product shows only provider-level status, users get inconsistent expectations. If your product shows normalized platform-level status, support volume drops.
Settlement timing and state translation
State translation is the core job of orchestration. You need deterministic mapping between provider states and internal states: initiated, authorized, pending settlement, available, locked, reversed, failed, disputed, finalized. Without this translation, downstream systems cannot reason reliably.
This is why fiat and crypto integration is less about connector count and more about transactional semantics. Teams that solve semantics early can add providers later with less risk.
Comparison table: fiat vs crypto transaction behavior
| Dimension | Fiat rail behavior | Crypto rail behavior | Platform implication |
|---|---|---|---|
| Core model | Account/intermediary based | Network confirmation based | Requires state normalization |
| Reversibility | Often possible via institutional processes | Usually difficult after finality | Needs explicit risk rules |
| Status granularity | Provider-specific lifecycle | Chain-specific lifecycle | Needs orchestration mapping |
| Settlement window | Often delayed or batched | Varies by chain load/finality rules | Impacts available balance logic |
| Evidence source | PSP/acquirer/issuer logs | On-chain tx + node data | Needs unified audit evidence |
3) Compliance and Auditability Require Normalized Operations
Many teams underestimate compliance friction in crypto fiat integration. They focus on onboarding checks and sanctions tooling, then discover later that operational evidence is inconsistent across rails. Regulators, auditors, and internal controls do not care which provider gave which status; they care whether your platform can explain financial events coherently.
A compliant platform needs policy consistency, traceability, and decision evidence at platform level. Provider logs are inputs, not the final evidence model.
AML workflow differences across rails
AML logic differs by transaction path. Fiat flows rely heavily on account context and institutional counterparties. Crypto flows add chain analytics context, wallet screening, and counterparty ambiguity in certain scenarios. Teams need one policy framework that can evaluate both paths without duplicating control logic.
This is where orchestration and policy engines should work together. Orchestration standardizes event shape. Policy engines apply context-dependent controls. The platform should not need separate compliance universes for each rail.
Accounting normalization and modern reporting
If you want modern accounting compatibility, you need normalized financial events. The ledger cannot store “provider says settled” as accounting truth. It should store platform-defined accounting states backed by evidence references and reconciliation outcomes.
This approach reduces reconciliation disputes and improves close cycles. It also enables cleaner separation between operational balances, safeguarded funds, pending settlements, and recognized revenue components.
4) Stablecoin Operations Add Hidden Complexity
Stablecoins are often presented as simple settlement accelerators. In practice, stablecoin operations create multidimensional complexity: token standards, chain variants, fee markets, bridge assumptions, and custody constraints. Supporting one stablecoin ticker is not equivalent to supporting one stablecoin operation model.
A robust fintech platform with crypto capabilities should treat stablecoin support as a product of policy, treasury, and infrastructure, not only wallet transfer logic.
Same asset label, different operational behavior
USDC on one chain is not operationally identical to USDC on another chain. Fee behavior, confirmation timing, ecosystem tooling, and monitoring reliability can differ materially. If you abstract this too aggressively without policy controls, you create hidden risk.
Platform teams should define chain-specific policies for minimum confirmations, monitoring latency thresholds, fee tolerance, route eligibility, and incident response triggers. Asset support should be gated by operational readiness, not market demand alone.
Stablecoin treasury and synchronization overhead
Stablecoin settlement can improve speed, but treasury still needs synchronization between on-chain positions and fiat obligations. If token inflows/outflows are not reconciled into a unified balance model in near real time, liquidity decisions become reactive.
This is where many teams discover that “crypto support” was the easy part, while synchronization, controls, and reporting become the real long-term workload.
“Vendor relationships can make or break a product’s success.” — Fintech Garden episode 110
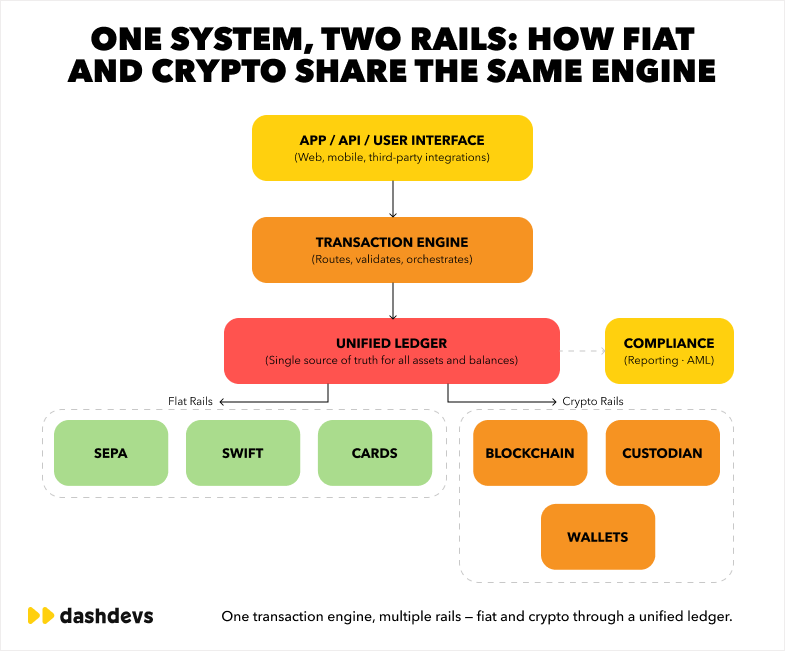
5) Unified Orchestration Layer
If you want to understand how to build a fiat crypto platform that scales, start with orchestration. The orchestration layer is the operational brain between external rails and internal business logic. It translates provider behavior into platform behavior.
Without orchestration, every product feature couples directly to provider specifics. With orchestration, product teams work against stable internal contracts while integration teams manage provider diversity behind abstractions.
What orchestration should own
The orchestration layer should own routing decisions, state normalization, retry policies, idempotency controls, timeout handling, and error classification. It should also expose consistent APIs and event contracts to wallet, risk, ledger, and support tools.
In a mature hybrid fintech platform, orchestration also enforces operational safeguards such as rail eligibility, risk-based route selection, and fallback behavior when one provider degrades.
Why abstraction is a business control, not only an engineering pattern
Provider abstraction reduces replacement cost and increases negotiation leverage. More importantly, it protects business continuity. If one processor, chain node provider, or fiat onramp degrades, orchestration can reroute flows according to policy.
This is not theoretical. It is one of the few practical ways to prevent single-provider incidents from becoming platform-wide outages.
Table: fragmented integrations vs orchestration-first architecture
| Architecture model | Typical behavior under growth | Operational outcome |
|---|---|---|
| Direct point-to-point integrations | Every new provider adds unique edge cases to product logic | Slow releases, fragile support workflows |
| Partial abstraction | Some normalized states, but many provider-specific exceptions leak | Moderate velocity, recurring incidents |
| Orchestration-first | Provider differences handled in one control layer | Faster integration cycles, consistent operations |
6) Unified Transactional History and Balance Visibility
Users, support teams, and auditors all ask the same question in different language: what happened to this money, and what is its current state. A platform cannot answer that reliably if history is split across provider dashboards and chain explorers without normalization.
A unified balance system depends on unified transactional history. One without the other is incomplete.
One timeline across rails
A strong event model represents each transaction as one timeline with multiple evidence points: initiation, provider acknowledgement, risk decisions, settlement progression, finality, reversals, and customer-facing status updates.
This is where unified ledger design and orchestration intersect. Ledger should store authoritative state transitions. Orchestration should ingest, map, and validate external events before those states are committed.
Why visibility matters for product and finance
Product teams need visibility to reduce user friction. Finance teams need visibility for reconciliation and reporting. Risk teams need visibility for anomaly detection. If each team depends on different data sources, decisions diverge and accountability weakens.
Unified history fixes this by creating one reference model for all functions. It does not remove complexity, but it contains complexity in one governed operational model.
7) Real-Time Ledger Design for Hybrid Rails
A multi-account ledger system is usually the backbone of scalable hybrid infrastructure. It should not be treated as passive storage. It is the control plane for balances, postings, state transitions, and accounting evidence.
For teams planning build multi currency fintech app initiatives, ledger design is where future scale is either enabled or constrained.
Ledger architecture requirements
At minimum, the ledger should support deterministic postings, idempotent event handling, balance partitioning, holds/reserves, reversal logic, and explainable state transitions. It should also support asset and account abstractions for fiat and crypto without losing audit clarity.
If your platform includes a multi asset wallet and a multi currency wallet, ledger models must separate representation from control. Displayed balances can be aggregated by UX rules, while accounting balances remain explicitly partitioned by asset, entity, and state.
Reconciliation and treasury visibility by design
Real-time does not mean “every event is final instantly.” It means reconciliation state is continuously updated and traceable. Treasury should see available, pending, reserved, and in-transit positions in one model with explicit confidence and evidence markers.
This approach reduces end-of-day surprises and supports better liquidity planning. It also enables earlier incident detection when expected and observed settlement patterns diverge.
To understand why this pattern becomes non-negotiable at scale, this deep dive on multi-account ledger system is directly relevant.
8) Business Logic Orchestration Engine in Practice
The orchestration engine coordinates external and internal systems: banking APIs, card processors, blockchain movements, stablecoin settlement paths, ledger postings, and risk actions. In a mature platform, this engine is policy-driven and observable.
This is the operational center of fiat crypto app software where product intent is translated into executable transaction behavior.
Scenario: fiat funding to crypto purchase to card spend
Consider a typical journey in a fintech app with crypto integration: user funds account via fiat rail, converts to stablecoin, then spends via card-linked balance. Without orchestration, each step has isolated states and brittle handoffs. With orchestration, one transaction policy graph governs eligibility, limits, rate windows, and posting sequence.
The result is predictable behavior across channels and cleaner support resolution when incidents occur.
Scenario: chain congestion with fallback policy
When chain conditions degrade, a policy-aware orchestration layer can delay, reroute, or reprice within approved limits while preserving customer transparency. It can also apply risk flags that temporarily restrict high-volatility flows.
This is where engineering and operations align. The platform is not “down”; it is operating under controlled degraded mode with explicit rules and auditable decisions.
9) Why This Matters for Product and Infrastructure Teams
For leadership, the value of unification is speed plus control. For teams, the value is reduced cognitive load and fewer operational contradictions. Engineers build against stable contracts. Product managers ship with clearer constraints. Finance and risk teams operate with one financial truth.
If your roadmap includes crypto banking platform development or omni-banking solutions, unification should be treated as a first-order product requirement.
Provider flexibility and infrastructure ownership
When orchestration and ledger layers are strong, provider changes become operational projects, not product rewrites. This gives teams flexibility to optimize costs, coverage, and reliability over time.
This is one reason many companies evaluate a white label fintech platform model early: they want infrastructure ownership patterns without rebuilding everything from scratch.
Faster integration loops for new capabilities
Unified infrastructure shortens delivery cycles for new rails and products. Adding a new fiat onramp, expanding a stablecoin route, or launching card-linked spend with card issuing services becomes easier when state, policy, and posting models already exist.
Teams that skip this foundation often move fast at first and then slow down due to integration drag, reconciliation overhead, and incident handling complexity.
10) DashDevs and Fintech Core: Infrastructure Experience in Hybrid Systems
DashDevs focuses on architecture where one operational model supports both fiat and crypto rails. The objective is straightforward: preserve product flexibility while increasing control over balances, settlements, and operational evidence.
For teams asking how to build a fiat crypto platform with realistic scaling assumptions, we normally start with target operating model design before connector implementation. This avoids expensive rework later.
What we build in practice
A typical delivery scope includes orchestration contracts, provider abstraction, transaction state taxonomy, ledger posting model, reconciliation flows, treasury visibility modules, and internal tooling for support and operations. We also define policy ownership boundaries so compliance and risk controls remain auditable.
This model supports progressive expansion: start with one conversion flow, one wallet model, one reporting baseline, then scale to additional assets, rails, and entities without splitting financial truth.
How Fintech Core fits the architecture
Fintech Core is used as modular infrastructure for teams that need practical acceleration without sacrificing operational clarity. It is especially relevant where product teams must integrate fiat and crypto services while preserving one consistent balance and transaction model.
For context on infrastructure evaluation in adjacent domains, this review of core banking solutions can help frame build-vs-platform decisions.
Operational credibility over presentation layers
A platform can look modern and still be operationally brittle. DashDevs prioritizes reliability patterns: deterministic event handling, idempotency, posting consistency, reconciliation observability, and transparent support tooling. These are the controls that keep scaling costs predictable.
If you need specialized wallet implementation depth, an experienced ewallet app development company can shorten delivery while keeping infrastructure decisions consistent with long-term operating goals.
Operational Scenarios Product Teams Usually Underestimate
Most architecture documents look clean until real behavior enters the system: retries from third-party providers, users repeating taps, webhook delays, chain congestion, card reversals, and reconciliation cutoffs that do not align with customer expectations. The difference between a demo and a platform is whether these scenarios are first-class design inputs.
Teams often ask how to build a fiat crypto platform and focus on “happy path” flow diagrams. In production, failure-path discipline defines reliability. Below are scenarios that should be designed early, not deferred.
Scenario A: Deposit credited, conversion delayed
A user funds with fiat and immediately requests conversion to stablecoin. The fiat processor returns success quickly, but internal settlement confidence is still pending. If conversion proceeds without policy checks, treasury may temporarily over-allocate liquidity.
In an orchestration-first model, the transaction engine uses explicit state gating: funded-pending-settlement, funded-available, conversion-eligible. The user still sees transparent progress, but the platform avoids creating hidden mismatch between customer balances and treasury assumptions.
Scenario B: Stablecoin transfer confirmed, callback late
A chain transaction reaches confirmation target, but provider callback arrives late or duplicated. Systems without idempotent orchestration may post balance twice or trigger support alerts unnecessarily.
A robust design treats chain proof and provider callback as separate evidence channels that map into one normalized event stream. Posting logic is idempotent. Reconciliation checks evidence completeness and flags unresolved variance before close cycles.
Scenario C: Card authorization accepted, capture reversed
This is a classic intermediary edge case in card flows. Authorization succeeds, customer sees completed action, then downstream reversal arrives due to merchant capture logic or acquirer timeout rules.
If platform state is tied directly to a single processor status, customer trust deteriorates. If orchestration tracks authorization, capture, and reversal as separate states with clear UX language, support and finance teams can resolve quickly without narrative confusion.
Scenario D: Multi-chain stablecoin support without policy partitioning
Product introduces support for the same stablecoin on two chains. Fees, confirmation timing, and operational incident patterns differ materially. Without chain-level policy partitioning, risk controls become inconsistent and hard to audit.
The safer approach is to treat each chain route as a distinct operational lane with explicit eligibility rules, settlement thresholds, fee tolerance, and monitoring SLAs. Asset naming can stay user-friendly while internal control remains route-specific.
Migration Blueprint: From Fragmented Rails to Unified Operations
Most teams do not start greenfield. They inherit PSP connectors, internal balance tables, manual reconciliation scripts, and partially documented support workflows. Migration strategy matters as much as target architecture.
A practical migration path for building fiat crypto platform operations should be incremental. Replace critical control points first, then consolidate surrounding workflows.
Phase 1: Define the operational truth model
Create a canonical transaction state model that can represent both fiat and crypto lifecycle events. Do not start with UI labels. Start with operational states required by treasury, compliance, support, and accounting.
This model should include explicit transitions, terminal states, evidence references, and reversal semantics. Once this is stable, orchestration and ledger teams can align implementation details without constant redefinition.
Phase 2: Introduce orchestration as a compatibility layer
Instead of replacing all providers at once, place an orchestration service in front of existing integrations. The goal is to standardize inbound and outbound contracts while current rails continue operating.
This compatibility layer should handle status mapping, idempotency keys, timeout policy, retry strategy, and basic route governance. Product teams can then consume normalized APIs while migration proceeds behind the interface.
Phase 3: Move posting authority to the ledger core
In many legacy stacks, provider callbacks directly mutate balances. That pattern should be phased out. The ledger should become the only posting authority, with orchestration submitting verified events.
This shift improves traceability and reduces balance drift. It also allows consistent controls for holds, reserves, prepayment flows, and release logic regardless of whether funds originated via fiat onramp or blockchain transfer.
Phase 4: Consolidate reconciliation and treasury views
Once event normalization and posting authority are in place, reconciliation can move from spreadsheet-driven matching to event-driven variance analysis. Treasury dashboards can display available, pending, in-transit, and at-risk balances across rails.
This is where business value becomes visible. Finance closes faster, support cases resolve with clearer evidence, and risk teams can detect anomalies earlier with less manual triage.
Migration anti-patterns to avoid
| Anti-pattern | Why it fails | Better alternative |
|---|---|---|
| Rebuilding all integrations before state normalization | Delays value and multiplies rework | Normalize states first, migrate rails gradually |
| Letting providers remain posting authority | Creates balance inconsistency risk | Ledger as single posting authority |
| Treating reconciliation as reporting-only | Variance discovered too late | Near real-time reconciliation controls |
| Ignoring support tooling during migration | Incident resolution degrades | Build investigator tools in parallel |
Risk, Drawbacks, and Trade-Offs You Should Plan Explicitly
A unified architecture does not remove trade-offs. It changes where trade-offs are managed. Teams that pretend there are no drawbacks usually shift risk from engineering to operations.
Design quality comes from acknowledging limits early and setting policy boundaries that are explicit, auditable, and practical.
Limited usability vs controlled risk
Some routes will remain restricted to a single merchant or a controlled environment for compliance or liquidity reasons. That can feel like a product limitation, but it may be the right risk posture at a given stage.
The important part is explicit communication. Users can accept limited usability when the platform is transparent. They do not accept hidden constraints that surface as unexplained failures.
Vendor lock-in and obsolescence risk
Every integration carries lock-in risk. A proprietary provider API can accelerate launch but increase migration cost later. This is why abstraction and contract stability are not “nice-to-have” architecture ideals; they are strategic safeguards.
The same applies to obsolescence risk. A provider that is operationally strong today may be strategically misaligned tomorrow. If your platform cannot reroute quickly, business strategy becomes dependent on external product roadmaps.
Privacy concerns and data minimization
Unified operational visibility should not become uncontrolled data expansion. Privacy concerns increase when teams aggregate events without clear purpose boundaries.
A mature model uses role-based access, purpose limitation, and auditable retrieval paths. Unified history can coexist with strict data governance when access design is intentional.
Contactless and channel-specific complexity
If your roadmap includes contactless flows, EMV card usage, QR code payment, NFC interactions, or mobile order and pay journeys, channel behavior should be explicitly represented in the event model. Otherwise, channel-specific failures appear as generic transaction errors and degrade support quality.
In hybrid systems, channel details are often the hidden cause of mismatch between customer perception and financial state. Good orchestration preserves channel context as part of financial evidence.
Implementation Checklist for the First 180 Days
If you are planning how to build a fiat crypto platform with real operational constraints, the first six months should focus on control foundations, not feature breadth.
The checklist below is intentionally practical and biased toward execution.
0–60 days: architecture and policy baseline
- Define canonical transaction states for fiat and crypto rails.
- Define posting authority and idempotency strategy.
- Define reconciliation control points and variance thresholds.
- Define routing and fallback policy for each provider.
- Define customer-facing status taxonomy aligned with operations.
61–120 days: controlled production scope
- Launch one primary fiat onramp flow and one conversion path.
- Run orchestration and ledger with full observability enabled.
- Deploy support tooling with transaction drill-down and evidence links.
- Validate accounting mappings with finance before high-volume rollout.
- Implement incident runbooks for provider degradation and chain delays.
121–180 days: scaling readiness
- Add secondary route coverage behind same orchestration contracts.
- Expand treasury dashboards with route-level liquidity segmentation.
- Introduce chain-specific policy sets for stablecoin operations.
- Tune risk controls using observed behavior and false-positive data.
- Freeze and test close-cycle reporting under peak load scenarios.
If your roadmap includes multi-rail payouts, custody-adjacent controls, or cross-entity treasury operations, this is usually where platform teams evaluate whether to deepen custom build or evolve with infrastructure modules from a white label fintech platform.
Fragmented vs Unified: Quick Decision Matrix
| Question | Fragmented stack answer | Unified stack answer |
|---|---|---|
| Can you explain one transaction across rails? | Usually not without manual reconstruction | Yes, through one normalized timeline |
| Can treasury see one real-time position model? | Partial and delayed | Structured and near real-time |
| Can product ship new rail integrations quickly? | Slows down over time | Faster with orchestration contracts |
| Can accounting close cleanly under growth? | High manual effort | Lower friction with normalized posting |
| Can support resolve disputes quickly? | Cross-tool investigation needed | Single transaction narrative |
Conclusion
Hybrid financial ecosystems are becoming the default operating context for many fintech products. Users expect one experience. Finance teams expect one balance truth. Regulators expect one explainable control model. None of those expectations are satisfied by connector sprawl.
The practical lesson is clear: rails matter, but orchestration matters more than rails themselves. Supporting crypto is technically feasible for most teams. Unifying operations across fiat and crypto rails is where architecture, product design, and operational maturity must converge.
If you are serious about how to build a fiat crypto platform that can scale beyond pilot stage, prioritize unified transaction orchestration, unified balance design, and accounting-compatible evidence models from the start. That is what protects velocity as complexity grows.
DashDevs works with teams that need this kind of infrastructure ownership, and Fintech Core is designed for platforms that want modular, scalable, and operationally consistent financial systems across hybrid rails.

