Non-Custodial Wallets for Mobile Apps: What Web3Auth Enables for Fintech and Web3
Summary
Non-Custodial Wallets in 60 Seconds
- Non-custodial wallets put asset ownership with the user; for fintech products, they are becoming infrastructure—not a crypto sidebar feature.
- Web3Auth and similar stacks reduce onboarding friction by replacing seed-phrase-only flows with social, MFA, and MPC-style key handling while keeping users in control.
- The strategic shift is structural: wallets behave like a new account layer—connect a wallet instead of opening an account, programmable money alongside traditional rails.
- UX and architecture matter more than which chain you pick; poor custody and integration design creates support debt, compliance gaps, and rework.
- DashDevs builds wallet-ready fintech alongside core banking, BNPL, and open banking—so custody choices stay aligned with product, risk, and regulation.
- Board-level success means TCO clarity, KPIs (support cost per wallet, activation, recovery), and alignment with FATF-style expectations and regional rules such as MiCA—not only shipping a wallet SDK.
Financial software has a recurring pattern: a new channel appears, boards ask for a roadmap slide, and teams underestimate what it costs to run safely at scale. Non-custodial wallets sit in that pattern today—not because every company must issue keys, but because ownership, programmability, and mobile distribution now intersect with regulated fintech in ways that affect distribution, unit economics, and risk. From years of building and advising fintech products, the same lesson applies: the expensive failures are rarely consensus algorithms; they are custody boundaries, operations, and messaging that outrun legal reality.
This piece is written for founders, C-suite owners, and senior product and engineering leaders who already speak P&L and delivery fluently. The aim is a business frame for where Web3Auth-class tooling fits, what it does not replace, and how to avoid treating wallet work as a feature ticket instead of infrastructure.
Why non-custodial wallets are becoming core fintech infrastructure

Market narrative and operating reality should be separated. The narrative is that crypto wallets are ubiquitous; the operating question is whether wallet software earns a place beside core banking and payments budgets because it changes distribution, unit economics, or risk in a measurable way.
Independent research is easy to misread when headlines are cherry-picked. Analyst work should be used directionally, not as a single source of truth. Grand View Research’s crypto wallet market analysis, for example, models the broader crypto wallet category—hardware and software, multiple operating-system contexts—and points to sustained expansion through the 2030s, with mobile adoption and DeFi-adjacent usage among recurring drivers. Segment definitions differ across firms, so anchoring a board decision to one CAGR number is fragile. Anchoring it to direction is not: wallet infrastructure is a growing line of business for vendors, institutions, and consumer platforms that need signing, custody UX, and chain connectivity at scale.
What matches that direction in the field is behavior: wallet interactions—sign, pay, prove, hold—are now ordinary product verbs across investing, loyalty, and cross-border use cases. Self-custodial connection patterns still dominate many on-chain analytics snapshots; treat such percentages as directional, not laboratory precision, but the product implication is stable—large parts of Web3 distribution are wallet-first.
Strategic interpretation for boards
This is not “crypto up” as entertainment. Four structural shifts show up in serious planning conversations:
- Account layer — “Connect wallet” competes with “create account” as the front door for certain products and partnerships.
- Ownership — Programmable ownership splits the stack: regulated fiat and compliance in internal systems; on-chain assets and proofs where the model requires it.
- Programmability — Signed messages and contracts become integration surfaces next to ISO messages, cards, and bank APIs.
- Embedded finance — Organizations integrate wallet + chain next to traditional rails, unless the license forbids it or the thesis does not require it.
In digital banking platforms DashDevs delivers, onboarding, KYC, and account infrastructure still define how people enter regulated services. Non-custodial capability extends that story with user-controlled assets and chain-native flows—without pretending EMI, banking, or adjacent obligations disappear. The design question is always boundary: what the ledger owns, what the chain owns, and how the organization proves they agree under audit.
“As fintechs evolved, their once-simple models became multi-layered ecosystems.” - Fintech Garden episode 122
Takeaway: wallets are no longer only crypto tools. For a growing set of behaviors, they are becoming a primary interface—the way bank accounts anchored the last wave of fintech, now alongside cards, account-to-account rails, and instant payments.
For how traditional and emerging wallet patterns combine without fragmenting delivery, see fintech software development.
Board-level questions before funding wallet work
Strip the deck to three tests. If the answers are vague, the organization is not ready to debate vendors or chains—only to waste calendar:
- Revenue thesis — Does a wallet unlock revenue or partnerships that cannot be reached through custodial APIs and partners—or is the initiative mostly brand signaling?
- TCO — What is the fully loaded three-year cost: engineering, security, support, nodes, compliance, vendor lock-in—not SDK line items alone?
- Stress ownership — Who owns the customer when devices are lost, networks congest, providers fail, or sanctions questions surface?
Weak answers mean product discovery should precede another integration sprint.
Custodial vs non-custodial: what finance and legal need to align on
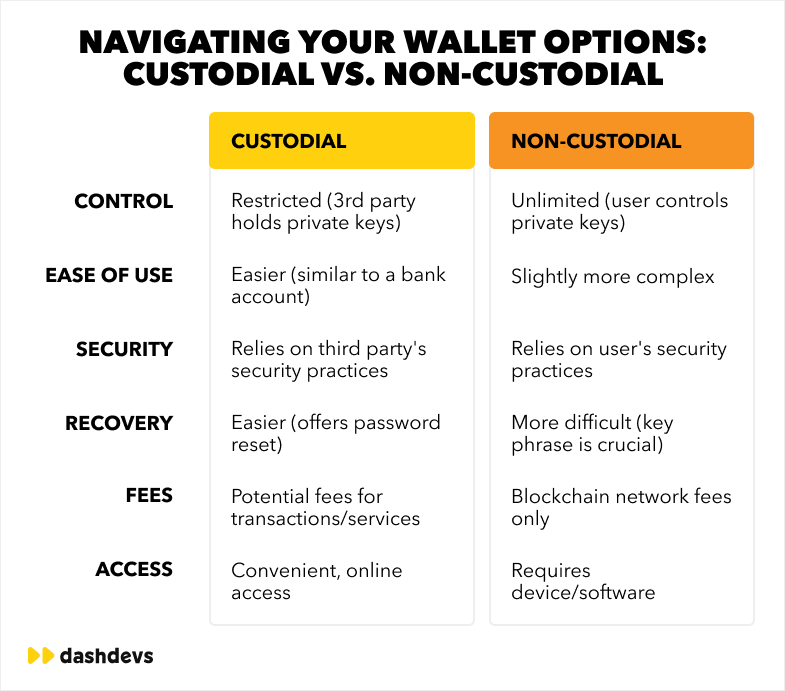
Custodial models mean the firm or a licensed partner holds keys and settlement responsibility for users under a defined regulatory frame. Non-custodial means users hold keys—directly or through user-centric MPC—and the product facilitates signing and experience. The vocabulary is short; the P&L and legal surface area is not.
| Factor | Custodial | Non-custodial |
|---|---|---|
| Ownership vs responsibility | Platform carries operational burden; users delegate | Users own keys; the product still owns UX, education, recovery design |
| Compliance vs flexibility | Easier to unify KYC, AML, ledger narrative | More on-chain freedom; harder to align with fiat bridges and licensing |
| UX vs scale | Familiar account metaphors | Demands strong UX or churn explodes |
| Recovery | Resets and support playbooks | Recovery without negligent central honeypots is a discipline |
| Speed to market | Often faster with licensed rails | Faster for pure on-chain flows; slower when reconciliation is heavy |
| Investor narrative | Clear regulated custody story | Strong “user-owned” story; requires precise legal language |
Custody is an architecture decision. It touches payment gateway services, ledger design, support economics, and how investors diligence the company. Choosing non-custodial because it sounds modern—without a use case—buys cost without differentiation.
P&L reality: custodial models often centralize measurable operations: omnibus constructs, reconciliation teams, adapted dispute workflows. Non-custodial pushes cost into client software, recovery, education, and chain operations—often under-budgeted in year one. Neither model is universally cheaper; they produce different cost structures and different support curves.
Hybrid patterns that hold up under audit
Strong regulated teams rarely treat the world as binary. They ship custodial fiat and cards, then add non-custodial or MPC modules for specific assets. They use embedded wallets for UX while settlement still touches licensed partners. The operational win is explicit reconciliation: what the core ledger says, what the chain says, and how drift is detected before finance or regulators do.
“Vendor relationships can make or break a product’s success.” - Fintech Garden episode 110
Key infrastructure is a long-term partner choice. Selection criteria should assume years of operation, not a single pilot quarter.
Why non-custodial UX fails—and which metrics actually matter
End users are not trying to “learn Web3.” They are trying to complete jobs: invest, send, earn rewards, prove membership, move value. Non-custodial flows fail for predictable business reasons, not because “people do not get crypto.”
Onboarding friction still drives the largest drop-off. Seed phrases are cognitively expensive. Forced backup too early kills activation; skipped backup kills retention when devices change. Strong products use progressive security: deliver value, then deepen assurances—especially in retail mobile contexts where attention spans are short.
Seed phrases remain appropriate for advanced users; they are a weak default for mass-market fintech. Support economics begin to resemble password-reset volume—except outcomes can be irreversible.
Trust is what spreadsheets are underweight. Users trust brands and clear outcomes. If signing feels like approving a black box, repeat usage collapses regardless of how impressive the protocol metrics look in a pitch deck.
DashDevs treats this as product craft and UI/UX development: human-readable outcomes, explicit failure recovery, language aligned with banking mental models—not only DeFi-native jargon.
Metrics that reflect business health
“Taps to sign” is a poor north star. Leadership should prefer repeat behavior: second successful transaction rate, support tickets per thousand active wallets, and recovery success after device change. When support intensity resembles retail banking without banking margins, non-custodial was often the wrong shape for that segment—regardless of technical correctness.
What Web3Auth-class infrastructure actually solves
Web3Auth (formerly Torus) is best understood as wallet infrastructure for authentication and key management, not as a consumer wallet brand that users must install separately. Vendor capabilities evolve; production decisions require current documentation and security review. The business problem this category addresses is stable: shrink the distance between familiar login and user-controlled signing.
What it is
APIs and SDKs for embedded wallet creation tied to identities users already accept—email, social, MFA—often using MPC or distributed key approaches depending on configuration. That is materially different from opening every journey with a raw seed phrase.
How it works at the decision level
Users authenticate through channels they already trust; the stack provides keys and session material the application uses to sign and connect. Recovery becomes a product design space—not only a paper backup.
Why it matters commercially
It compresses time-to-credible wallet UX, which affects conversion, referral, and cost-to-serve—provided internal architecture does not fight the flow.
What it explicitly does not replace
It does not replace the risk engine, ledger, KYC policy, or AML stack. It does not confer compliance. It supports integration of identity and signing in an auditable way when boundaries are clean.
At DashDevs, wallet work sits beside KYC, cards, and core flows. Fintech Core reflects how boundaries are drawn: Web3Auth-class tools address identity-to-key bridging; the institution still owns policy, reconciliation, and regulated truth.
Business impact: revenue, cost, risk, and positioning
Revenue. Wallet-native models can unlock fees, tokenized perks, partnerships, and protocol integrations where law allows. Boards should not greenlight on novelty alone; they should require a path to ARPU, LTV, and margin after support.
Cost. Embedded infrastructure can reduce some centralized custody costs in specific architectures—but it reallocates spend to reliability, nodes, audits, and vendors. Fragmented ledger vs chain truth—without reconciliation discipline—erodes margin the same way it does in payment integration programs.
Risk. The fastest way to lose trust is marketing copy that outruns legal reality. Compliance and legal should review self-custody language before launch—not after social media has already promised absolutes.
Strategy. Owning the wallet relationship can be defensible when the category shifts on-chain. Thin wrappers around someone else’s API, without UX and policy depth, rarely are.
| Board lens | Question leadership should answer |
|---|---|
| Growth | Does this unlock distribution or partnerships that cannot be reached otherwise? |
| Margin | What is infra + support cost per active wallet at target scale? |
| Risk | What is the position on lost keys, sanctions, and travel-rule-class flows? |
| Defensibility | Does the company own UX, policy, and data—or only a thin integration? |
Line worth repeating: wallets are infrastructure, not features. A backlog checkbox does not fund recovery, incidents, or regulatory mapping.
Does the roadmap need a non-custodial wallet?
Treat this as a product-context filter—the three board-level tests earlier in this article (revenue thesis, TCO, stress ownership) still apply first. The table below only answers when a non-custodial shape is more likely to fit, once those tests are passed.
| Product context | Typical guidance |
|---|---|
| Neobank, no on-chain thesis | Stay custodial / partner-led until the use case is concrete |
| Investment / tokenized settlement | Strong candidate; reconcile ledger and chain early |
| Cross-border with stable settlement needs | Strong candidate; compliance before raw chain speed |
| Loyalty with portable digital value | Often hybrid; portability may favor user-controlled designs |
| Pure fiat BNPL / credit | Avoid chain complexity unless the product thesis demands it |
Readiness means: a one-sentence use case the board understands; a jurisdiction map; UX for loss and failure; a named operational owner for incidents—same bar as in Board-level questions before funding wallet work.
Workshop scorecard (one hour)
Rate each dimension 1–5: use case clarity, regulatory fit, UX maturity beyond the happy path, documented engineering boundaries, operational readiness. Totals below 15 usually mean the organization is still in discovery—not execution.
When that is the case, product discovery is the right investment—not another chain integration.
Architecture: where the wallet layer lives in the stack

A wallet layer is not a sidecar experiment. It sits alongside authentication, limits, policy engines, and—typically—a traditional ledger for fiat.
| Component | Typical responsibility |
|---|---|
| Mobile client | Clear prompts, limits, error copy aligned with legal |
| API gateway | AuthN/Z, rate limits, correlation IDs |
| Wallet orchestration | Signing workflow, policy, vendor adapters |
| Ledger (fiat/core) | System of record for regulated balances |
| Nodes / RPC | Submission, health, failover |
| Indexers | Event history, reconciliation inputs |
Regulated connectivity at scale—exemplified by Tarabut gateway—shows the same discipline wallet integrations need: contracts, monitoring, operational ownership.
Delivery usually involves backend development services and solution architecture services so fiat, chain, and partner boundaries remain coherent as the product grows.
“Instead of building a bank from scratch, companies can partner with BaaS providers to access pre-built banking infrastructure.” - Fintech Garden episode 108
The parallel for wallets: teams compose infrastructure for keys and nodes—they rarely succeed by inventing cryptography in a first release.
Data, privacy, and audit
Security and legal stakeholders should be engaged early: how wallet events land in the data warehouse, what audit trail regulators expect, and whether PII around devices and addresses is minimized. If signing logs exist only in a vendor dashboard, operational posture is weaker than the demo suggests.
Integrating wallets without breaking the core product
A wallet integration is not a side API. It touches identity, money movement semantics, support tooling, and often two sources of truth (ledger vs chain). When those seams are weak, the core product still “works” in demos while operations quietly rot: duplicate users, wrong balances in CRM and support consoles, and month-end reconciliation that finance cannot sign off without manual heroics.
Most failures cluster at three seams: identity ↔ address mapping, transaction lifecycle, and API orchestration between mobile, backend, and wallet vendors. The sections below are what strong programs nail before scale—not after production traffic arrives.
Seam one: identity and address mapping
Every user record must map cleanly to wallet address(es) and to any custodial or fiat identifiers the product already uses. Ambiguity here is how support ends up with “two accounts” for one person, or how risk sees activity that cannot be tied back to a KYC file.
Concrete failure pattern: A user logs in with email, creates a wallet, then reconnects later with a different auth path. Without a single canonical internal user key and strict merge rules, the product creates a second profile—or worse, links the wrong address to marketing and limits.
What to standardize early:
- One internal customer ID that never forks across auth methods.
- Explicit rules for multiple addresses (per chain, per purpose) and which one is primary for statements and support.
- Audit fields: when an address was bound, from which device, and through which vendor.
Seam two: transaction lifecycle—not just “pending / done”
On-chain transactions are state machines. They can be submitted, dropped, replaced, stuck pending, reorged in edge cases, or succeed after retries. The mobile UI and the core ledger must share vocabulary: what “failed” means, what the user should do next, and what support is allowed to promise.
Concrete failure pattern: The app shows “success” because the client received a hash, while the backend never indexed confirmation; support refunds or compensates based on app state instead of reconciled state. That is how small UX gaps become P&L leaks.
Minimum lifecycle discipline:
- A single canonical status model in the backend (not only in the client).
- Webhook or polling pipelines that align with indexer reality; backoff when RPCs degrade.
- Idempotency on “submit transaction” and “create wallet” APIs so retries do not fork state.
Seam three: API orchestration and vendor boundaries
Web3Auth or any wallet-auth vendor is part of a chain: mobile ↔ your APIs ↔ vendor ↔ nodes/indexers. If every squad calls nodes directly, there is no place to enforce policy, logging, or rate limits—and incidents become forensic exercises.
Partner treatment means SLAs, fallback when authentication fails, expected behavior under chain congestion, and documented escalation paths (who pages whom, which runbooks exist). Those expectations belong in writing before launch, not after the first customer-visible outage.
Orchestration layer responsibilities typically include: signing policy (what users may sign, at what limits), fee or gas strategy, routing to the right RPC/indexer, and correlating vendor request IDs with internal traces.
Copy, legal truth, and support alignment
Wallet copy must match legal and risk truth: “you control your keys” is not a harmless tagline if the actual model includes custodial steps, partners, or recovery paths that imply shared control. Business stakeholders—not only engineers—should review signing screens, error strings, and email templates.
Support runbooks need the same language as the product: what agents can see (hashes, statuses, limits), what they cannot promise, and when to escalate to risk. Otherwise, the core brand absorbs reputational damage from wallet edge cases the CRM was never built to explain.
Environments, keys, and release discipline
Sandbox behavior diverging from production is a classic source of “works in demo, breaks at go-live.” Contract tests between your canonical APIs and vendor adapters catch shape changes before deploy. Secrets and API keys must be scoped per environment; shared keys between sandbox and production are a common audit finding.
Integration readiness checklist (leadership view)
| Area | Question to answer before scaling traffic |
|---|---|
| Identity | Is there one internal customer ID and explicit address-binding rules? |
| Lifecycle | Does the backend own truth for tx status—not only the mobile client? |
| Reconciliation | How does chain state map to ledger or liability records monthly? |
| Vendors | Are SLAs, escalation paths, and fallback auth behavior documented? |
| Support | Do agents have tooling and language aligned with legal reality? |
For broader integration discipline, fintech integrations and fintech architecture remain useful references—wallet sprawl fails the same way undisciplined API sprawl fails: fast demos, expensive operations.
Web3Auth versus alternatives: patterns, not permanent rankings
Vendor landscapes shift; the table below describes patterns for discussion with engineering and legal—not a static scorecard.
| Pattern | Strength | Trade-off |
|---|---|---|
| Web3Auth | Embedded wallets, social login, strong mobile/web developer UX | Vendor economics at scale; chain coverage varies by configuration |
| Embedded (e.g., Privy-class) | Product-led onboarding for crypto-native apps | Custody model and regions require legal review |
| Email-first (e.g., Magic-class) | Low friction | Compare key model to the firm’s definition of non-custodial |
| WalletConnect + external wallets | Users bring existing wallets | Less onboarding control; stronger for DeFi-native audiences |
| In-house | Maximum control | Highest security and compliance burden |
Vendor criteria that belong in RFPs
Custody model, regions and data residency, chain coverage versus roadmap, recovery paths, and exit cost. The integration strategy should define what it takes to swap providers without rewriting customer journeys.
Cost: total cost of ownership, not demo day
A working demo proves integration is possible; it does not prove the business can afford to run the product for three years. Total cost of ownership (TCO) for wallet-adjacent fintech splits into build, launch, and steady state—and most underestimates land in steady state, where nodes, support, audits, and policy work never stop.
What typically sits in the TCO stack
One-time or project-heavy: architecture and threat modeling for key flows, penetration testing, vendor security questionnaires, smart-contract or signing-flow review where applicable, and integration hardening (sandbox parity, idempotency, reconciliation jobs).
Recurring and scaling: RPC/node or indexer fees (often per environment and per region), observability and alerting, on-call rotation, vendor fees tied to MAU or signatures, KYC and monitoring stack consumption, legal retainer for product changes, and periodic re-certification when vendors or chains upgrade APIs.
People time (often under-modeled): trained L2 support for wallet tickets, risk operations for edge cases, and engineering hours for chain forks, deprecations, or incident postmortems. A non-custodial product can shift work from centralized ops to client and partner coordination—without reducing total human load if UX is weak.
Example: how a phased budget usually breaks down (illustrative)
These bands are illustrative—every license and geography differs—but they help boards see where money disappears after the MVP:
| Phase | What leadership is funding | Typical focus |
|---|---|---|
| 0–6 months | MVP wallet UX, one chain, one auth path, basic monitoring | Speed and learning |
| 6–18 months | Second chain or asset type, hardened recovery, reconciliation automation | Drift from “demo” to “production” |
| 18–36 months | Multi-region, higher SLA, deeper compliance automation, vendor renegotiation or migration option | Scale and risk reduction |
If phase two was never budgeted, leadership discovers that “we shipped a wallet” actually meant “we shipped a prototype with production traffic.”
Using app-build economics as a baseline—then stress-testing them
Baseline product economics vary widely; how much does it cost to build an app is a useful reference for build ranges and hidden line items. For anything that touches keys, treat security and integration as multipliers on those estimates, not equal-weight line items next to a generic API.
The TCO question to put in every investment memo
If RPC prices double and support tickets per thousand users do not fall, what happens to gross margin in month eighteen? If there is no answer, the TCO model is incomplete.
KPIs and risk metrics leadership should review together
A wallet line that cannot be measured is an experiment subsidized by the rest of the business. The mistake is tracking on-chain vanity metrics while ignoring support cost, recovery success, and compliance queue depth—then wondering why margin collapses after launch.
Product and finance metrics (one scorecard)
These metrics answer whether the wallet is a business, not a feature.
| Metric | What it signals | Example of “bad” |
|---|---|---|
| Activation → first successful sign | Whether onboarding actually works | High drop-off after login but before first sign—often UX or chain config |
| Wallet MAU / DAU | Engagement versus gimmick | MAU flat while marketing spend rises—wallet not part of a habit loop |
| Support tickets per 1k wallet users | Cost-to-serve | Approaching retail-banking ticket rates without banking revenue per user |
| Failed transaction rate | UX and infrastructure health | Spikes during gas spikes or RPC outages—infra not production-grade |
| Recovery success after device change | Whether the model survives real life | High “I lost access” contacts—recovery design failed the mainstream user |
| Revenue per active wallet | Unit economics | Revenue only from interchange elsewhere—wallet not pulling its weight |
| Time-to-complete critical flows | Friction | P95 signing latency drives abandonment in payments use cases |
Example (composite): A retail investment app sees first sign completion at 40% but second transaction at 8%. Product blames “users”; the real issue is often signing copy, fee disclosure, or stuck “pending” states—fixable with UX and lifecycle orchestration, not a new chain.
Risk and compliance metrics (same meeting, same deck)
Risk metrics belong in the same review as product KPIs—otherwise compliance becomes a parallel theater.
| Risk metric | Why leadership should care |
|---|---|
| Sanctions / PEP hits on linked addresses or counterparties | Direct regulatory exposure |
| Manual review queue depth and age | Operational drag and user churn |
| False positive rate on automated flags | Support cost and reputational harm |
| Travel-rule-class or VASP messaging failures | Potential regulatory findings or partner cutoff |
| Incident count involving signing, keys, or vendor auth | Signal of architecture or vendor maturity |
Compliance is part of unit economics: every hour risk teams spend on preventable exceptions is margin walking out the door.
Cadence: how often to review
Early in launch, a weekly product+risk slice (30 minutes) beats a monthly vanity dashboard. At scale, monthly business reviews with the same KPI definitions—definitions that do not change when the numbers look bad—keep the organization honest.
Compliance and risk: the non-negotiable frame
Non-custodial is not a synonym for “unregulated.” It changes where keys live, not whether AML, sanctions, or consumer protection apply when fiat, intermediaries, or business models touch regulated activity.
FATF, VASPs, and the global baseline
International expectations on virtual assets and VASPs set the floor for how serious institutions plan. The FATF virtual assets hub is a practical starting point for AML/CFT reading. FATF’s work on stablecoins and unhosted wallets is especially relevant when products enable P2P transfers or self-custody without centralized intermediaries (report). None of this replaces counsel—it defines the questions boards should expect auditors and partners to ask.
MiCA and EU go-to-market
In the EU, MiCA shapes how crypto-asset services can be offered and communicated to consumers. The Commission’s MiCA overview is a practical entry for product and legal alignment. Wallet UX and marketing claims must match MiCA reality: vague “decentralized” language is a liability when the actual service includes custodial steps, partners, or restricted activities.
Travel rule and information flows
Where travel-rule-style obligations apply, the product must know who is sending value to whom—not only that a hash settled on-chain. Teams that treat on-chain transfers as “anonymous by default” often discover late that VASPs, banks, or scheme rules require structured information flows. That affects architecture: what metadata you capture, when you block submission, and how you evidence decisions under audit.
KYC, AML, and monitoring—still on the critical path
Organizations should map: how identity links to addresses; how sanctions screening applies to counterparties and address lists; how monitoring covers high-risk patterns; and how marketing claims match legal fact. Specialist KYC services belong in the same program as engineering—not as a post-launch patch when a regulator asks uncomfortable questions.
Example: fiat on-ramp without a coherent story
A common failure mode is: users on-ramp with a card or bank transfer, then move assets to a non-custodial path. If the KYC story for the on-ramp does not connect cleanly to on-chain activity monitoring, the organization ends up with two partial pictures of risk. Leadership should insist on one risk narrative and one data model—even if vendors differ.
Governance: who decides when rules shift
Regulation will continue to move faster than internal slide decks. Strong programs assign ownership: who interprets policy changes, who updates customer terms, who retrains support, and who signs off on new jurisdictions. Wallet products fail when engineering ships quickly but governance is undefined—especially when a single social post promises “full self-custody” that the license and tech stack cannot support.
How DashDevs approaches wallet-ready fintech
DashDevs treats wallet capability as part of the same delivery system as core banking, payments, and mobile—not as an isolated experiment. Product, legal, risk, and engineering share one program; custody language, architecture, and operations are designed together so the live product matches what the board approved.
The modular capability view is summarized in Fintech Core; broader delivery patterns appear in fintech software development. The case snapshots below are not “wallet-only” projects—they show how identity, connectivity, money movement, and trustworthy UX must align when non-custodial or chain-adjacent features sit next to regulated rails.
Digital banking platform: identity, onboarding, and the account layer
The digital banking platform case reflects how DashDevs builds onboarding, KYC, and account infrastructure at scale. That discipline transfers directly to wallet programs: the same rigor applies to who the user is, how they recover access, and how support explains money movement. A non-custodial layer that bypasses those standards creates two onboarding experiences—and two support models.
InABLR investment platform: when signing and money movement must feel institutional
The InABLR investment platform illustrates complex investment UX—flows where users must trust outcomes, understand state (“pending,” “settled,” “failed”), and reach support without chaos. Wallet integrations fail for the same reasons when signing screens are opaque or transaction lifecycle is unclear. The lesson for Web3Auth-class rollouts: clarity and state machines matter as much as key management.
Tarabut gateway: regulated connectivity as a blueprint for orchestration
The Tarabut gateway case shows regulated API connectivity and product UX meeting at scale. Wallet orchestration—nodes, webhooks, retries, reconciliation—benefits from the same operational discipline: contracts with partners, monitoring, incident playbooks, and clear ownership. Teams that treat wallet providers as “set and forget” repeat the failures open banking integrations avoided only after hard lessons.
Cross-border payments: compliance before chain speed
Cross-border payment solutions sit at the intersection of FX, licensing, and messaging rules. Stablecoin or on-chain settlement does not remove those constraints—it re-sequences them. DashDevs uses this lens when clients ask for “fast international transfer”: the travel-rule-class and sanctions reality is modeled before chain selection, not after users are live.
BNPL and embedded credit: keeping credit logic and new rails aligned
BNPL app development work matters when wallet events could be misread as repayment or delinquency signals—or when programmable settlement touches merchants. Credit policies and on-chain events must reconcile to one customer truth; otherwise operations and collections break under edge cases.
Outlook: tokenization, identity, and regulation
The next several years will not be defined by a single “winning chain.” They will be defined by which products earn the right to move value under clearer rules, with identity and wallet UX that mainstream users can tolerate.
Tokenization and programmable settlement
Tokenization of real-world assets, loyalty, and receivables will keep pulling wallets into mainstream fintech—not only as speculation, but as distribution and liquidity mechanics. Boards should ask what problem tokenization solves for the customer (speed, access, transferability) and whether the firm can operate the lifecycle—corporate actions, disputes, tax reporting—not only mint an asset.
Identity: passkeys, platform logins, and the blur with “sign”
Passkeys and platform identity APIs continue to blur login and signing. That is good for UX and difficult for security reviews: the attack surface shifts toward device compromise, session hijacking, and social-engineering of recovery. Wallet roadmaps should include identity architecture as a first-class workstream, not an afterthought bolted onto Web3Auth or any other vendor.
Regulation: MiCA, FATF evolution, and national stablecoin rules
Policy and product must share a timeline—MiCA, FATF, and national stablecoin / VASP rules are covered in Compliance and risk: the non-negotiable frame; this outlook section only highlights trajectory, not duplicate legal detail. Analyst outlooks—including Grand View Research’s crypto wallet perspective—remain directional evidence for capital allocation, not precision instruments.
What to watch on a 2026–2028 roadmap
Signals that beat TPS charts: institutional participation in tokenized markets, interop standards for identity and messaging, and enforcement patterns in major jurisdictions. Wallet infrastructure rarely pays back inside twelve months—capital and talent need a watch list, not a hype cycle.
At a glance
- Liquidity & counterparties — pilots vs repeatable settlement; who actually provides depth and SLAs.
- Interop — identity, address ownership, cross-chain messaging; can the journey survive standard shifts?
- Enforcement & narrative — cases and guidance where you market and settle, not only where you’re incorporated.
- Vendor economics — consolidation, exit clauses, who owns keys/metadata/audit logs.
- Cadence — quarterly reviews with an owner and a pre-read, or the roadmap stays a slide deck.
Liquidity and counterparties
- Watch for tokenized cash, money-market instruments, fund shares, and repurchase-style plumbing moving from pilots to repeatable settlement—with named custodians and clearing expectations.
- Pressure-test the roadmap: if on-chain liquidity only exists in demo environments, distribution partners will reprice or walk.
- Ask explicitly: who is the buyer of last resort? What are redemption SLAs? Which venues sit inside sanctions and travel-rule screening—not which chain has the newest bridge.
Interop as a product bet
- Expect identity attestations, address ownership, and cross-chain messaging to keep evolving—and vendors to deprecate paths.
- Decide whether your customer journey can absorb breaks when standards shift (pair with the identity workstream above: passkeys and sign semantics).
- Remember: interop is not only bridges—it is support, disputes, and audit evidence when the path spans Web2 login, MPC signing, and on-chain settlement.
Enforcement and narrative risk
- Track how regulators and prosecutors signal intent—cases and guidance updates matter as much as new statutes.
- Map enforcement where you market, onboard, and settle—not only the entity’s domicile.
- Avoid roadmap language (“borderless,” “permissionless” self-custody) that outruns license facts; it becomes liability under basic scrutiny.
Vendor and stack economics
- Plan for consolidation among wallet infrastructure, node vendors, and compliance tooling as stacks narrow to approved lists.
- Front-load exit clauses and portability: who owns keys, metadata, and audit logs—switching cost explodes after volume and integrations are live.
Operating cadence
- Run quarterly reviews covering: liquidity and partner assumptions, interop changes hitting UX, enforcement headlines needing legal interpretation, vendor roadmap deprecations.
- Assign an owner and require a pre-read—otherwise the roadmap is a document, not a decision system.
Conclusion
Non-custodial wallets change who holds keys, how users enter the product, and how trust is built. Web3Auth-class tooling can materially improve adoption and key orchestration—but market discipline and regulatory alignment mean business owners must own the risk narrative. That work cannot be delegated to a single engineering spike or a vendor slide deck.
If wallets are infrastructure, they deserve infrastructure funding: architecture, compliance, UX, operations, and metrics. The organizations that win treat wallet decisions as P&L and governance decisions—and treat vendors and chains as execution detail, not strategy by default.

